
Boosting Cybersecurity Adoption: How Good UX Can Make a Difference
IIIMPACT is a leading product UX design and development company with over 17 years launching 100s of digital software enterprise and mobile products for startups to Fortune 10 companies. We have helped clients from almost every industry vertical — energy, robotics, fintech, cybersecurity, retail, HR, education, eCommerce, etc.
We’ve also been listed in theInc5000twoconsecutive years in a row for one of the fastest growing independent companies in the US. We’ve also ranked in the top 50 in the southwest which includes Texas/Dallas / Houston / Austin, Nevada / Las Vegas, and Arizona / Scottsdale.
If you are looking for a top product design and development company to help launch or redesign your enterprise, SaaS, mobile, POS, or web application with a scalable, high-quality Design and DevOps process —contact IIIMPACT
Cybersecurity Software
Cybersecurity is critical for safeguarding sensitive data and assets against cyber threats. However, for many users, the complexity and unfamiliarity of these tools can make them difficult to use and understand. This is where user experience (UX) design comes in.
By using UX design when making software design, companies can make products that are not only safe but also easy to use, which will lead to more people adopting and using the software.
In this article, we will explore how top cybersecurity companies like IBM Security, Microsoft, Cisco, Oracle, Palo Alto Networks, Checkpoint, and Fortinet can incorporate good UX strategy and design into their development process.
By having a good product strategy and process, the product will be easier to use, users will be happier, and it will be easier to find, analyze, and fix threats. This higher productivity and lower cost will make their software more valuable, leading to more people using it.
What are the top cyber security companies missing with UX design?
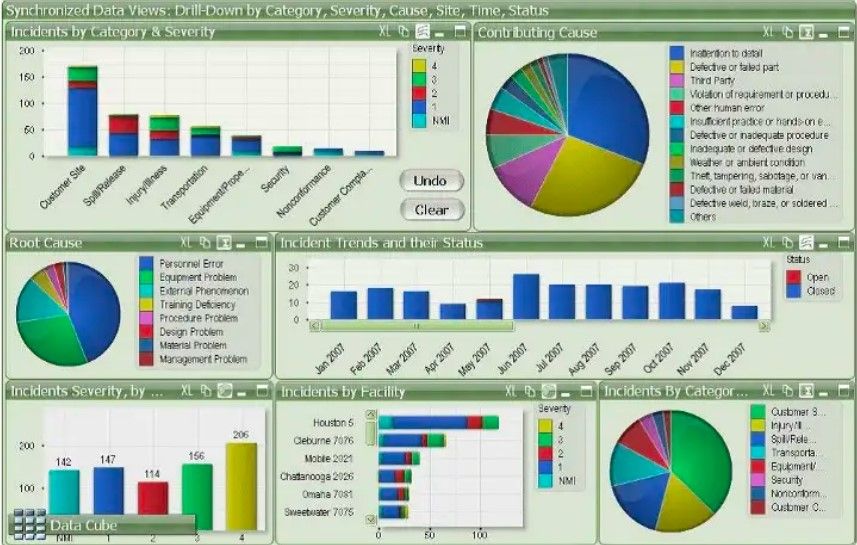
Fugly Dashboard
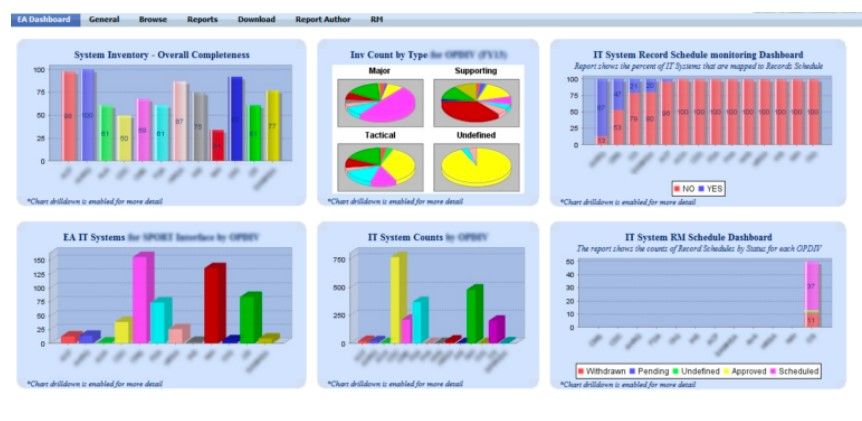
Fugly Dashboards 2 – The Sequel
All of these companies are well-known in the cybersecurity industry. They offer a wide range of products and services to protect businesses and organizations from cyber threats.
Some of their users, though, have said that the software is hard to use and understand.
By building a good UX strategy and design into the development process, they can make their software easier to use, leading to more people adopting and using it.
Cybersecurity software is critical for protecting sensitive information and assets from cyber threats. This can make security less safe because users might not know about important security features or might not know how to use the software correctly. However, for many users, the complexity and unfamiliarity of these tools can make them difficult to use and understand.
This is where user experience (UX) design, user interface (UI) design, and usability research come in. By incorporating these practices into the development of cyber security software, companies can create products that are not only secure but also user-friendly.
UX design is the process of making products that give users experiences that are meaningful and useful. In the context of software dess, this means designing softwaredesign that is easy to navigate, understand, and use. One way to achieve this is through clear and intuitive UI design.
Usability research is another important aspect of creating user-friendly cyber security software tools. To do this, test the software on actual users to identify any bugs or design flaws.This can include issues such as confusing navigation, unclear labels, or confusing error messages. By doing usability research, companies can find these problems and fix them to make the user experience as a whole better.
Why UX design and UI design are important?
One of the key advantages of using UX design, UI design, and usability research while developing software is that more people will use and accept the software. When users find the software difficult to use or understand, they are less likely to use it.
Another benefit of good UX design and usability research is that it can lead to increased efficiency and productivity. When software is user-friendly and easy to use, users can complete tasks faster and with fewer errors. This can lead to increased productivity and reduced costs for companies.
In addition to these benefits, including UX design, UI design, and usability research in the development of software decan lead to higher customer satisfaction and NPS scores.
What is Net Promoter Score
NPS is a customer loyalty metric that measures customers’ willingness to not only return for another purchase or service but also make a recommendation to their family, friends or colleagues.
It is a powerful and effective technique, that can greatly increase a company’s revenue if used properly.
The key advantages of NPS are that it has a strong correlation with business growth and that it is simple to gather, analyze, and disseminate.
Cybersecurity Software User Experience Metrics
Scores above 0 are typically regarded as good, and scores above 50 as excellent.
Check out some of the NPS scores of these top cybersecurity companies:
Fortinet -Score 8– Fortinet is an American multinational corporation headquartered in Sunnyvale, California. They make and sell security software, appliances, and services, such as firewalls, anti-virus software, intrusion prevention, and endpoint security. It is the fourth-largest network security company by revenue.
Michael and Ken Xie, brothers, developed Fortinet in 2000. It raised about $93 million in funding by 2004 and introduced ten FortiGate appliances. That same year was the beginning of a recurring patent dispute between Fortinet and Trend Micro. The company went public in 2009, raising $156 million through an initial public offering. During the 2000s, Fortinet added products for things like wireless access points, sandboxing, and secure messaging, among other things.
Splunk Score 8–Splunk is an American multinational corporation based in San Francisco, California, that produces software for searching, security auditing, and analyzing machine-generated big data, via a web-style interface.
Splunk gathers, connects, and indexes real-time data in a searchable repository. It can then use this data to make graphs, reports, alerts, dashboards, and visualizations.
Splunk’s goal is to make machine data available across an organization by finding data patterns, giving metrics, diagnosing problems, and giving threat intelligence for business operations.
Oracle 25–Oracle specializes in developing and marketing computer hardware systems and enterprise software products. A carefully compiled list of well-known brands indicates that Oracle is ranked 173rd on the World Best Brands list. In comparison to other tech companies, Oracle fares better by ranking #43 amongst its main rivals.
Additional Top Cybersecurity Companies NPS Scores
IBM 27 – IBM (International Business Machines Corporation) is an American multinational technology company headquartered in Armonk, New York, United States, with operations in over 170 countries. IBM is a company that was founded in 1911 and later renamed “International Business Machines” in 1924.
Secureworks 31–Secureworks® (NASDAQ: SCWX), a global cybersecurity leader with Dell Technologies, enables customers and partners to outpace and outmaneuver adversaries on the dark web with precision, so they can rapidly adapt and respond to market forces to meet their business needs.
Cisco 38 –is an American multinational technology conglomerate headquartered in San José, California, in the center of Silicon Valley, that develops, manufactures, and sells networking hardware, telecommunications equipment, and other high-technology services and products.
As you can see, the NPS scores aren’t the greatest, but these are the leading companies in cybersecurity today.
Is that why it seems like every time you turn around, there’s a new breach?
For example, making users make long, complicated passwords or using two-factor authentication can be frustrating and take a lot of time, which can lead to resistance and people not following the rules.
Paypal hacked—35000 PayPal accounts breached in credential stuffing attack
TMobile breached— 37 Million accounts
When your cyber security analysts are happy with the software they are using, they are more likely to recommend it to others and continue using it in the future. This can lead to increased sales and revenue for companies.
Using UX design, UI design, and usability research when making cybersecurity software design can lead to a number of benefits, such as more people using and adopting the software, more efficiency and productivity, and happier customers.
The Challenge of Cybersecurity Software Design
Cybersecurity software design presents a unique set of challenges for UX designers. The main goal of UX design is to make an interface that is easy to use and makes sense. However, the security needs of cybersecurity software can sometimes conflict with this goal.
Also, cybersecurity software often has complicated and technical interfaces that make it hard for people who aren’t tech-savvy to understand and use it well. This can make it hard for people to use the software because they might feel overwhelmed or scared by it.
To address these challenges, UX designers must find a way to balance the security requirements of cybersecurity software with the principles of good UX design. By doing so, they can create software that is both secure and user-friendly, making it more likely that users will adopt and use the software consistently.
The Importance of UX Design for Cybersecurity
Good UX design is essential for boosting cybersecurity adoption for several reasons:
User-Friendly Interfaces Encourage Adoption
When cybersecurity software is designed with good UX principles, users are more likely to find the software user-friendly and easy to use. This makes it easier for people to use, and people are more likely to use software that is easy to understand and use. Also, software that is easy to use can cut down on user mistakes and make the software work better, making it more likely to protect against attacks.
Reduced Friction Increases Compliance
Users of cybersecurity software often have to follow certain security protocols, like making passwords that are hard to guess or using two-factor authentication. However, these requirements can create friction for users, which can lead to non-compliance. By designing interfaces that are easy to use and understand, UX designers can reduce friction and make it more likely that users will comply with security protocols.
Improved Engagement Increases Security
When cybersecurity software is fun to use and easy to understand, users are more likely to use it regularly. This can lead to more consistent use of the software, which can lead to better security in the long run. For instance, a user who is interested in their password manager is more likely to use it regularly, which makes it harder for hackers to get into their accounts.
Designing for Accessibility
Accessibility is another important part of UX design, and it can be especially important for security software. Cybersecurity threats can affect anyone, regardless of their age, ability, or background. UX designers can help make sure that everyone can get the protection they need by making software that can be used by a wide range of people.
5 must-have Network Security Tools for Small Businesses
Malicious programs that can hurt a small business’s operations and reputation are becoming more and more common. Investing in the right network security tools can help protect small businesses from cyber-attacks, data breaches, and other malicious activities.t allows remote employees to connect to your network securely, protecting sensitive data from interception by hackers.
Here are 5 must-have network security tools for small businesses:
Firewall – A firewall is a type of web application security that monitors and controls network traffic based on predefined security rules. It is the first line of defense because it stops people from getting into your network without your permission.
Antivirus and Anti-malware – Antivirus and anti-malware software are essential in protecting your network from malicious software such as viruses, spyware, and Trojans. These security tools can detect, isolate, and remove malicious software from your system.
Virtual Private Network (VPN) – A VPN provides a secure, encrypted connection between two networks over the internet. I
Intrusion Detection System (IDS) – An IDS monitors network traffic for suspicious activities and alerts the security administrators if any malicious activity is detected. This can help prevent a cyberattack before it becomes a major threat to your network.
Patch Management – Keeping all software up to date is critical for preventing security vulnerabilities that can be exploited by cybercriminals. Patch management tools automate the process of identifying and installing up-to-date software, reducing the risk of cyberattacks on your network.
Comparing Top Cyber Security Software Solutions: Pros and Cons
Here are some pros and cons of the best cybersecurity tools available:
- Norton Security – Norton Security is a popular and well-established cybersecurity solution. It provides comprehensive protection against viruses, malware, and phishing attacks. Norton Security’s interface is easy to use, and it offers a range of security features to keep your data secure. However, Norton Security can be resource-intensive and may slow down your computer.
- McAfee Total Protection – McAfee Total Protection is another popular cybersecurity tool that provides data protection against viruses, cyber threats, and ransomware. It also includes security features such as a password manager and parental controls. McAfee Total Protection, on the other hand, can be expensive and may slow down older computers. McAfee Total Protection, on the other hand, can be expensive and may slow down older computers.
- Kaspersky Internet Security – Kaspersky Internet Security is known for its advanced security features, such as its firewall and anti-spam filters. It also includes a virtual keyboard to protect against keyloggers. But there has been a lot of talk about Kaspersky Internet Security because of claims that it has ties to the Russian government.
- Bitdefender Total Security – Bitdefender Total Security is a comprehensive cybersecurity solution that offers protection against all types of malware, including ransomware. It also includes a password manager and parental control. Bitdefender Total Security can be expensive, and it may not work well with some other programs.
- Avast Premium Security – Avast Premium Security offers robust protection against viruses, malware, and other online threats. It also includes security features such as a VPN and a password manager. However, Avast Premium Security has faced privacy concerns due to its data collection practices.
Why Off-The-Shelf Security Solutions May Not Be Enough for Your Business
Here are some reasons why off-the-shelf security solutions may not be enough for your business:
- Limited Customization – Off-the-shelf security solutions are designed to work for a wide range of businesses, but not every business is the same. Your business may have security needs that are different from others and can’t be met by a ready-made solution. Some vulnerabilities that could be used by cyberattacks may need to be fixed with customization, and off-the-shelf solutions may not be able to meet these needs.
- Not Scalable – As your business grows, so does your network. Off-the-shelf security solutions might not be able to grow with your business as it grows. There is a chance that these solutions won’t work with new devices, web apps, or users on your network. This can leave your business vulnerable to cyberattacks and costly data breaches.
- Limited Flexibility – Off-the-shelf security solutions are designed with a one-size-fits-all approach. They offer pre-packaged features that may not align with the unique needs of your business. This can make it hard to combine with other security solutions or tools that your business may already be using.
- Lack of Personalization – With off-the-shelf security solutions, you are not able to personalize your security settings. This means that your business might be using security features that aren’t needed or don’t offer enough protection. It’s important to tailor security settings to your business needs to maximize security.
- Limited Support – Off-the-shelf security solutions may not offer adequate support for businesses that need help with customization, integration, or ongoing maintenance. This can leave your business open to cyberattacks if your security solution is not set up and maintained properly.
Enhancing Your Cyber Security: A Guide to Selecting the Right Security Solutions
In today’s digital age, cyber security is more important than ever before. No matter how big or small a business is, it must put a high priority on cyber security tools to protect sensitive data and assets. But because there are so many security software options, it can be hard to choose the right one for your business. Here are some tips to guide you in selecting the right security software solutions for your business:
- Conduct a Risk Assessment – Before you can select the right security solutions for your business, you need to assess your risk profile. This includes identifying potential vulnerabilities and threats to your network, data, and assets. Conducting a risk assessment will help you to identify the areas that need the most attention and will guide you in selecting the right security solutions to address these risks.
- Choose a solution that aligns with your business needs. It’s important to choose a security solution that aligns with your business needs. This includes factors such as the size of your business, your industry, and the type of data you handle. For example, businesses that handle sensitive customer data, such as financial or healthcare information, will need a more robust security solution than a business that handles less sensitive data.
- Look for Comprehensive Solutions – The best security solutions offer comprehensive social network protection against a range of threats, including viruses, cyberattacks, ransomware, and phishing attacks. Look for solutions that protect your data in multiple ways, such as firewalls, intrusion detection, and antivirus software.
Additional Guide to Selecting the Right Security Solutions
- Choose a solution with User-Friendly Features – Security solutions can be complex, but it’s important to choose one that is user-friendly and easy to navigate. This will help make sure that your employees can use the solution well and reduce the chance that they will make a mistake that could lead to a security breach. This will help make sure that your employees can use the solution well and reduce the chance that they will make a mistake that could lead to a security breach.
- Consider the Cost – While cost shouldn’t be the only factor in selecting a security solution, it is an important consideration. Make sure to choose a solution that fits your budget and offers the best value for your investment. Remember that the cost of a data breach can be much higher than the cost of investing in a strong security solution.
- Consult with a Security Expert – Navigating the complex world of cyber security on your own can be difficult. You might want to work with a security expert who can help you choose the best security solutions for your business. Based on your unique needs and risk profile, a security expert can give you useful advice and tips.
Network Security 101: A Beginner’s Guide to Essential Security Tools
Network security is a critical component of modern-day businesses. As the number of cyberattacks keeps going up, companies must take steps to protect their networks and data. In this guide, we explain how software detects and removes any malware found on your system, protecting it from further damage. For people who don’t know much about network security, we’ll talk about the most important security tools. They can also take action to prevent the attack from succeeding, such as blocking the attacker’s IP address, which every business should have.
Firewall
A firewall is a network security tool that monitors incoming and outgoing traffic and prevents unauthorized individuals from accessing your computer system. By functioning as a barrier between your network and the internet, it helps protect you from possible harm.
Antivirus Software
Antivirus software is a program that scans your computer or network for malicious software such as viruses, trojans, and worms.
Intrusion Detection and Prevention Systems (IDPS): IDPS is a security tool that monitors your network traffic for any unusual activity or attack. It detects and alerts you to any suspicious network activity, such as brute force attacks, port scans, or unusual traffic.
Virtual Private Network (VPN)
A VPN is a tool that lets your computer or network connect to the internet in a safe and encrypted way. It helps protect your network from unauthorized access and eavesdropping. It is especially helpful for workers who don’t work in your office but still need to connect to your network.
Encryption is the process of converting data into a secret code that can only be read with a key. It is an essential tool for securing sensitive data, such as customer information, financial data, and intellectual property. Encryption protects your data from unauthorized access, even if it is intercepted during transmission.
In conclusion, network security is a critical component of every business. By implementing essential security tools such as firewalls, antivirus software, IDPS, Secure VPN, and encryption, you can safeguard your network and data from cyber targeted attacks. These tools give your network security a strong base, and if you use them, you can lower the risk of security breaches and protect your business’s reputation and bottom line.
Understanding some of the basics
Web software to use for building software applications
The type of web software to use depends on what the application being built needs and wants. Some common web software used in cybersecurity applications includes programming languages such as Python, Java, and C++, web frameworks such as Django and Flask, and various cybersecurity-focused libraries and tools such as Nmap, Wireshark, and Metasploit.
What software is used in cybersecurity?
Cybersecurity uses a wide range of software tools and applications, depending on the needs and goals of the organization or individual. Some examples of commonly used software in cybersecurity are:
- Antivirus software – used to protect against malware and viruses.
- Firewalls – used to control and continuous monitoring network traffic for web attack prevention.
- Intrusion detection and prevention systems (IDPS) – used to detect and prevent network attacks.
- Vulnerability scanners – used to identify potential security weaknesses and vulnerabilities in computer systems and enterprise networks.
- Penetration testing tools – used to simulate cyber attacks and assess the security of systems and networks.
- Security information and event management (SIEM) software – used to collect and analyze security-related data from various sources to identify online threats and anomalies.
- Encryption tools – used to secure data and communications by encoding them in a way that only authorized parties can access.
- Password managers – used to securely store and manage passwords.
- Virtual private network (VPN) software – used to create secure connections between remote devices and networks.
What exactly is user experience in cyber security?
User experience refers to the design and usability of security systems and tools. Lastly, applications with the goal of creating a positive and efficient user experience.
UX is important so that people will use security tools and applications properly. This will leave systems and data vulnerable to online threats.
In addition, UX in cybersecurity includes designing security systems with the user in mind. So that they are intuitive, easy to understand, and require minimal effort on the part of the user.
This can include designing security alerts and warnings that are clear and easy to understand. Additionally, creating intuitive user interfaces for security tools and making easy to report security incidents or suspicious activity.
By focusing on UX in cybersecurity, security professionals can help ensure that security measures are effective. Through the adoption and proper use of security tools and applications by users. While also promoting a positive user experience.
What is the most comprehensive cybersecurity solution?
No cybersecurity solution is perfect. The best way to protect an organization or an individual depends on their needs and goals.
A comprehensive cybersecurity solution typically involves a combination of tools and techniques, including:
- Firewall and network security measures to protect against unauthorized users and malware.
- Endpoint security solutions to secure individual devices and prevent attacks on them.
- Intrusion detection and prevention systems (IDPS) to detect and prevent network attacks.
- Security information and event management (SIEM) software to monitor and analyze security-related data from various sources.
- Vulnerability management tools to identify and address potential security weaknesses.
- Access and identity management solutions to control access to systems and data.
- Data encryption and cloud backup solutions to protect data from identity theft or loss.
In addition to technical measures, complete security software should include policies, procedures, and employee training. This is to help prevent errors and make sure that everyone is aware of security risks and best practices.
_____
IIIMPACT has successfully collaborated with hundreds of companies worldwide helping them create the best user experience, strategy, and product innovation and improving their DevOps and DesignOps processes for a coachable and scalable team.
We help companies create innovative products with a user-centered design process that ensures better user engagement, usability and UX so that your products succeed at scale.
There are a lot of risks and problems that come with launching a software product. Let us help you find your way around these problems and solve some of them so you can feel more confident during the process.
Please drop us a message if you have any questions or would like to see how we can help you create the next innovative product.